Master Juniper Cloud with Associate JN0-214 Prep: Your Gateway to Success
Which term identifies to which network a virtual machine interface is connected?
Correct : A
In cloud environments, virtual machines (VMs) connect to virtual networks to enable communication. Identifying the network to which a VM interface is connected is essential for proper configuration and isolation. Let's analyze each option:
A . virtual network ID
Correct: The virtual network ID uniquely identifies the virtual network to which a VM interface is connected. This ID is used to logically group VMs and ensure they can communicate within the same network while maintaining isolation from other networks.
B . machine access control (MAC)
Incorrect: The MAC address is a hardware identifier for a network interface card (NIC). While it is unique to each interface, it does not identify the network to which the VM is connected.
C . Virtual Extensible LAN (VXLAN)
Incorrect: VXLAN is a tunneling protocol used to create overlay networks in cloud environments. While VXLAN encapsulates traffic, it does not directly identify the network to which a VM interface is connected.
D . virtual tunnel endpoint (VTEP)
Incorrect: A VTEP is a component of overlay networks (e.g., VXLAN) that encapsulates and decapsulates traffic. It is used to establish tunnels but does not identify the virtual network itself.
Why Virtual Network ID?
Logical Isolation: The virtual network ID ensures that VMs are logically grouped into isolated networks, enabling secure and efficient communication.
Scalability: Virtual networks allow cloud environments to scale by supporting multiple isolated networks within the same infrastructure.
JNCIA Cloud Reference:
The JNCIA-Cloud certification emphasizes understanding virtual networking concepts, including virtual networks and their identifiers. Virtual network IDs are fundamental to cloud architectures, enabling multi-tenancy and network segmentation.
For example, Juniper Contrail uses virtual network IDs to manage connectivity and isolation for VMs in cloud environments. Proper configuration of virtual networks ensures seamless communication and security.
Virtual Networking Documentation
Juniper JNCIA-Cloud Study Guide: Virtual Networks
Start a Discussions
Click the Exhibit button.
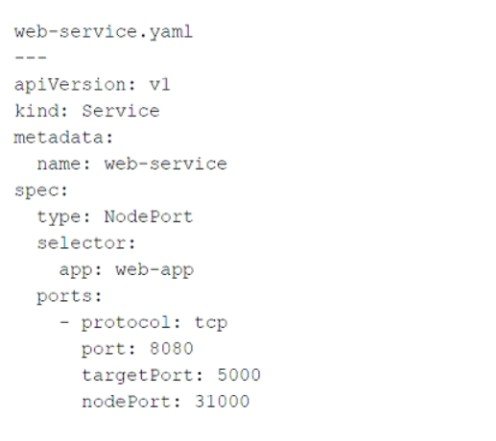
Referring to the exhibit, which port number would external users use to access the WEB application?
Correct : C
The YAML file provided in the exhibit defines a Kubernetes Service object of type NodePort. Let's break down the key components of the configuration and analyze how external users access the WEB application:
Key Fields in the YAML File:
type: NodePort:
This specifies that the service is exposed on a static port on each node in the cluster. External users can access the service using the node's IP address and the assigned nodePort.
port: 8080:
This is the port on which the service is exposed internally within the Kubernetes cluster. Other services or pods within the cluster can communicate with this service using port 8080.
targetPort: 5000:
This is the port on which the actual application (WEB application) is running inside the pod. The service forwards traffic from port: 8080 to targetPort: 5000.
nodePort: 31000:
This is the port on the node (host machine) where the service is exposed externally. External users will use this port to access the WEB application.
How External Users Access the WEB Application:
External users access the WEB application using the node's IP address and the nodePort value (31000).
The Kubernetes service listens on this port and forwards incoming traffic to the appropriate pods running the WEB application.
Why Not Other Options?
A . 80: Port 80 is commonly used for HTTP traffic, but it is not specified in the YAML file. The service does not expose port 80 externally.
B . 8080: Port 8080 is the internal port used within the Kubernetes cluster. It is not the port exposed to external users.
D . 5000: Port 5000 is the target port where the application runs inside the pod. It is not directly accessible to external users.
Why 31000?
NodePort Service Type: The NodePort service type exposes the application on a high-numbered port (default range: 30000--32767) on each node in the cluster.
External Accessibility: External users must use the nodePort value (31000) along with the node's IP address to access the WEB application.
JNCIA Cloud Reference:
The JNCIA-Cloud certification covers Kubernetes networking concepts, including service types like ClusterIP, NodePort, and LoadBalancer. Understanding how NodePort services work is essential for exposing applications to external users in Kubernetes environments.
For example, Juniper Contrail integrates with Kubernetes to provide advanced networking features, such as load balancing and network segmentation, for services like the one described in the exhibit.
Kubernetes Documentation: Service Types
Juniper JNCIA-Cloud Study Guide: Kubernetes Networking
Start a Discussions
You must provide tunneling in the overlay that supports multipath capabilities.
Which two protocols provide this function? (Choose two.)
Correct : B, D
In cloud networking, overlay networks are used to create virtualized networks that abstract the underlying physical infrastructure. To support multipath capabilities , certain protocols provide efficient tunneling mechanisms. Let's analyze each option:
A . MPLSoGRE
Incorrect: MPLS over GRE (MPLSoGRE) is a tunneling protocol that encapsulates MPLS packets within GRE tunnels. While it supports MPLS traffic, it does not inherently provide multipath capabilities.
B . VXLAN
Correct: VXLAN (Virtual Extensible LAN) is an overlay protocol that encapsulates Layer 2 Ethernet frames within UDP packets. It supports multipath capabilities by leveraging the Equal-Cost Multi-Path (ECMP) routing in the underlay network. VXLAN is widely used in cloud environments for extending Layer 2 networks across data centers.
C . VPN
Incorrect: Virtual Private Networks (VPNs) are used to securely connect remote networks or users over public networks. They do not inherently provide multipath capabilities or overlay tunneling for virtual networks.
D . MPLSoUDP
Correct: MPLS over UDP (MPLSoUDP) is a tunneling protocol that encapsulates MPLS packets within UDP packets. Like VXLAN, it supports multipath capabilities by utilizing ECMP in the underlay network. MPLSoUDP is often used in service provider environments for scalable and flexible network architectures.
Why These Protocols?
VXLAN: Provides Layer 2 extension and supports multipath forwarding, making it ideal for large-scale cloud deployments.
MPLSoUDP: Combines the benefits of MPLS with UDP encapsulation, enabling efficient multipath routing in overlay networks.
JNCIA Cloud Reference:
The JNCIA-Cloud certification covers overlay networking protocols like VXLAN and MPLSoUDP as part of its curriculum on cloud architectures. Understanding these protocols is essential for designing scalable and resilient virtual networks.
For example, Juniper Contrail uses VXLAN to extend virtual networks across distributed environments, ensuring seamless communication and high availability.
VXLAN RFC 7348
MPLSoUDP Documentation
Juniper JNCIA-Cloud Study Guide: Overlay Networking
Start a Discussions
Which two statements about containers are true? (Choose two.)
Correct : B, D
Containers are a lightweight form of virtualization that enable the deployment of applications in isolated environments. Let's analyze each statement:
A . Containers contain executables, libraries, configuration files, and an operating system.
Incorrect: Containers do not include a full operating system. Instead, they share the host system's kernel and only include the application and its dependencies (e.g., libraries, binaries, and configuration files).
B . Containers package the entire runtime environment of an application, including its dependencies.
Correct: Containers bundle the application code, runtime, libraries, and configuration files into a single package. This ensures consistency across different environments and eliminates issues caused by differences in dependencies.
C . Containers can only run on a system with a Type 2 hypervisor.
Incorrect: Containers do not require a hypervisor. They run directly on the host operating system and share the kernel. Hypervisors (Type 1 or Type 2) are used for virtual machines, not containers.
D . Containers share the use of the underlying system's kernel.
Correct: Containers leverage the host operating system's kernel, which allows them to be lightweight and efficient. Each container has its own isolated user space but shares the kernel with other containers.
Why These Statements?
Runtime Environment Packaging: Containers ensure portability and consistency by packaging everything an application needs to run.
Kernel Sharing: By sharing the host kernel, containers consume fewer resources compared to virtual machines, which require separate operating systems.
JNCIA Cloud Reference:
The JNCIA-Cloud certification emphasizes understanding containerization technologies, including Docker and Kubernetes. Containers are a fundamental component of modern cloud-native architectures.
For example, Juniper Contrail integrates with Kubernetes to manage containerized workloads, leveraging the lightweight and portable nature of containers.
Docker Documentation: Container Basics
Juniper JNCIA-Cloud Study Guide: Containerization
Start a Discussions
Which method is used to extend virtual networks between physical locations?
Correct : A
To extend virtual networks between physical locations, a mechanism is needed to transport network traffic across different sites while maintaining isolation and connectivity. Let's analyze each option:
A . encapsulations
Correct: Encapsulation is the process of wrapping network packets in additional headers to create tunnels. Protocols like VXLAN, GRE, and MPLS are commonly used to extend virtual networks between physical locations by encapsulating traffic and transporting it over the underlay network.
B . encryption
Incorrect: Encryption secures data during transmission but does not inherently extend virtual networks. While encryption can be used alongside encapsulation for secure communication, it is not the primary method for extending networks.
C . clustering
Incorrect: Clustering refers to grouping multiple servers or devices to work together as a single system. It is unrelated to extending virtual networks between physical locations.
D . load-balancing
Incorrect: Load balancing distributes traffic across multiple servers or paths to optimize performance. While important for scalability, it does not extend virtual networks.
Why Encapsulation?
Tunneling Mechanism: Encapsulation protocols like VXLAN and GRE create overlay networks that span multiple physical locations, enabling seamless communication between virtual networks.
Isolation and Scalability: Encapsulation ensures that virtual networks remain isolated and scalable, even when extended across geographically dispersed sites.
JNCIA Cloud Reference:
The JNCIA-Cloud certification covers overlay networking and encapsulation as part of its curriculum on cloud architectures. Understanding how encapsulation works is essential for designing and managing distributed virtual networks.
For example, Juniper Contrail uses encapsulation protocols like VXLAN to extend virtual networks across data centers, ensuring consistent connectivity and isolation.
VXLAN RFC 7348
GRE Tunneling Documentation
Juniper JNCIA-Cloud Study Guide: Overlay Networking
Start a Discussions
Total 65 questions
